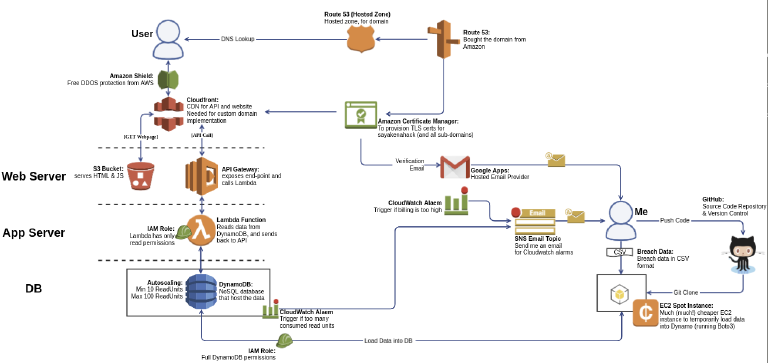
I keep this blog to help me think, and over the past week, the only thing I’ve been thinking about, was sayakenahack.
I’ve declined a dozen interviews, partly because I was afraid to talk about it, and partly because my thoughts weren’t in the right place. I needed time to re-group, re-think, and ponder.
This blog post is the outcome of that ‘reflective’ period.
The PR folks tell me to strike while the iron is hot, but you know – biar lambat asal selamat.
Why I started sayakenahack?
I'm one part geek and one part engineer. I see a problem and my mind races to build a solution. Building sayakenahack, while difficult, and sometimes frustrating, was super-duper fun. I don't regret it for a moment, regardless of the sleepless nights it has caused me.
But that’s not the only reason.
I also built it to give Malaysians a chance to check whether they’ve been breached. I believe this is your right, and no one should withhold it from you. I also know that most Malaysians have no chance of ever checking the breach data themselves because they lack the necessary skills.
I know this, because 400,000 users have visited my post on “How to change your Unifi Password”.
400,000!!!
If they need my help to change a Wifi password, they’ve got no chance of finding the hacker forums, downloading the data, fixing the corrupted zip, and then searching for their details in file that is 10 million rows long – and no, Excel won’t fit 10mln rows.
So for at least 400,000 Malaysians, most of whom would have had their data leaked, there would have been zero chance of them ever finding out. ZERO!
The ’normal’ world is highly tech-illiterate (I’ve even talked about it on BFM). Sayakenahack was my attempt to make this accessible to common folks. To deny them this right of checking their data is just wrong.
But why tell them at all if there’s nothing they can do about it? You can’t put the genie back in the lamp.