
Let’s first take a step back, and understand how and Internet Service Provider (ISP) like Telekom Malaysia, Maxis or Digi operate.

Let’s first take a step back, and understand how and Internet Service Provider (ISP) like Telekom Malaysia, Maxis or Digi operate.
Edweek.org further explains:
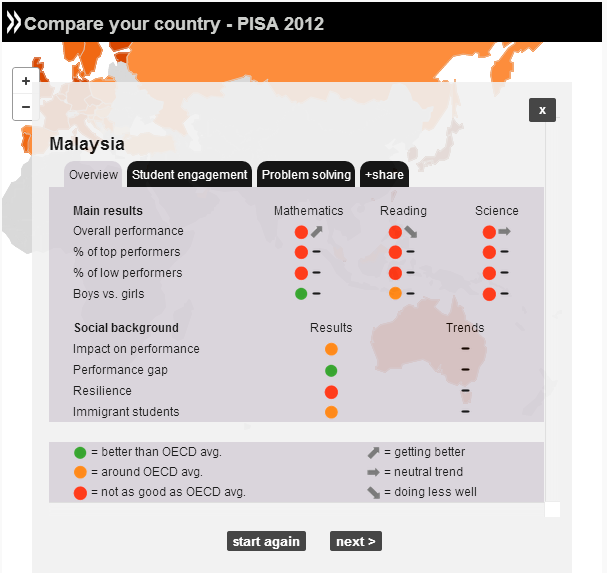
The assessment, which was the subject of an Organization for Economic Cooperation and Development (OECD) report released Tuesday, defined creative problem-solving as the ability to “understand and resolve problem situations where a method of solution is not immediately obvious.” Worldwide, a representative sample of 85,000 students took the exam, including 1,273 U.S. students in 162 schools.
As our thoughts and prayers remain with the passengers of flight MH370, I think that as the search enters its 3rd week, it’s a good time to reflect on just how much our perception of aviation technology has changed as a result.
It’s quite important to differentiate between what REALLY happens and what we THINK happens, an in some cases the gulf is so large, that our perception of what happens borders on science-fiction. Take for example, our perception of the US Secret Service. Years of Hollywood movies have led us to believe that if anyone even thought about firing a weapon at the President, Secret Service agents would immediately throw their bodies in the line of fire, evacuate the President and then take out the bad guy. That however is mere fairy tale–no different from the Giant Robots in Transformers or the Aliens in Star Wars. If you look at History and reality, you’d find that some years back, an Iraqi Gentleman not only had the time to throw a shoe at President Bush, but enough time to TAKE OUT A SECOND SHOE and throw it again at the President–were it not for the Presidents quick reflexes, he would have ended looking like David Beckham after a night out with Ferguson.
So the gulf between what we think the Secret Service CAN do, and what it ACTUALLY does, is quite enormous.

Here’s an age old question, is it pronounced router (as in rao-ter) or is it router (as in root-er).
A lot of people seem to think it depends where you are, if you’re in the US, it’s rao-ter, and if you’re in the UK it’s root-er. But the internet is global, it doesn’t care where you are, it doesn’t matter which culture you’re from, there can only be one answer to this question, and it must be location agnostic.
Tun Dr M, our beloved former Prime Minister, openly supports Israel–well sort off.
Today on his blog chedet.cc, he called on everyone to boycott Israel, stating quite clearly in his latest post that;
I think the whole world in the interest of justice should boycott doing business with Israel. This is truly a pariah state which is immoral and beyond the pale of human laws.
Now of course, you’re wondering if Tun Dr M supports Israel or not? Well in actual fact it’s both, because while his words say he opposes Israel, his actions, specifically those of his website suggest otherwise.
Internet users in Malaysia were reporting issues trying to access a specific page on the BBC UK website that was a hilarious post making fun of our ‘beloved’ Prime Ministers Kangkung remarks. Apparently the issue became so bad, that users took to social media –only to find that they were not alone. In fact, so many Malaysians were complaining that they couldn’t access the post, that the official twitter handle of the BBC News tweeted to its followers asking them if they had issues.
Are you in #Malaysia? Can you access this BBC story about #kangkung? http://t.co/sDKN4fFWyV - let us know using #BBCtrending— BBC News (World) (@BBCWorld) January 16, 2014
Now, I for one, experienced no such disruption–but then again I use a VPN, and quite frankly, so should you!However, there are a couple of things you need to know about internet censorship, and this debacle in particular.
Let’s be honest–Malaysians watch a lot of Porn.
On the outside, we may espouse our ‘Asian’ values and culture, but the cold-hard data suggest we’re as horny as the Japanese. In one of my past post, I showed how we have evidence of someone using the Government internet connection to download porn.
Today however, PornMD the self-proclaimed “biggest porn search engine” released statistics as to what Malaysians were searching on their site. The results aren’t that surprising, although I was quick shocked to see Tudung on there–apparently some people find it kinky.
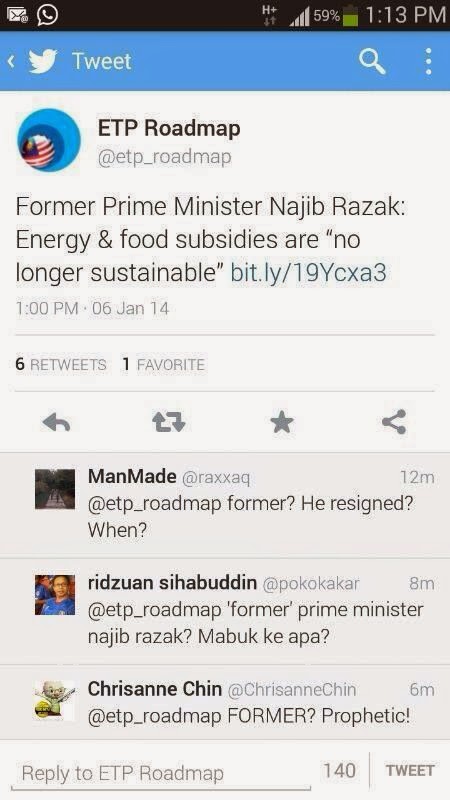
In case you’ve missed it. The official twitter handle of the ETP, @etp_roadmap, recently made a serious blunder. In a tweet sent out at 1.00pm on the 6th of January, they tweeted “Former Prime Minister Najib Razak: Energy and Food Subsidies are no longer sustainable”. Now the blunder of course was the word ‘Former’ and it was only a full one hour later (or an eternity in twitter time) was the tweet deleted and an apology issued.
OK....I made a boo boo!
Actually my method of 'hacking' the Unifi modems has a ridiculously simple work-around. Unfortunately, when I published the findings I was absolutely convinced the workaround didn't work--I was wrong :(
Details about how I was mis-lead are unimportant for now (although I will explain it later on), for now I think the simplest way to address and to make yourself more secure (though not 100% secure) is to disable remote management of the router. Don't worry here's a step-by-step guide on how to do it.
So I was wondering if I should publish this, but I guess I have to. If you’re one of the 500,000 Unifi subscribers in Malaysia, you need to know that your stock router–is completely hackable. TM has left you literally hanging by your coat-tails with a router that can be hacked as easily as pasting a link. So I was struggling to figure out if I really should have made this post, but in the end I think it’s better for you (and everyone else) to know just how easy it is to Hack Unifi accounts–not so you can hack them, but so that you can take some precautions over the situation.
But first, some caveats–everything I’m showing here is already public knowledge, the only difference is that I’ve culled and aggregated knowledge from different streams to show you just how easy an attacker can circumvent your password protection on your Unifi Dlink DIR-615 router, which is the stock router that comes with Unifi. It’s better for you to know about it than to remain oblivious to possibility that anyone from anywhere in the world, sitting in their room with their pyjamas on, can log onto to your router and start doing some rather nasty stuff.
Second caveat, is that as a result of this, some ‘kiddy-hackers’ may see this post and now be empowered with the means to attack, that’s a risk I’m willing to take to allow for everyone to know about it, so that they can do something about it. Keeping everyone in the dark about vulnerabilities of their routers is not a good thing. Security works better when everyone has access to the same information, this is how security works, and if you don’t agree–well tough luck.
With that said, here’s how you use Shodan, and a well known exploit to hack Unifi. The final exploit which doesn’t require any knowledge of the passwords starts at 4:08
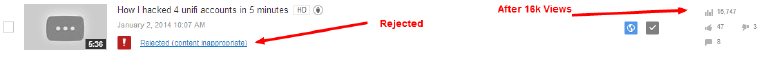
Update 22-Jun: My Apologies: YouTube have removed my video because someone reported it as being inappropriate. I am appealing..I’m not sure what about the video was inappropriate, and I have made no attempt to mis-lead anyone. Stay tuned. I’ve updated the video with a Vimeo upload instead.
Hacking Unifi Dlink routers using Shodan from Keith Rozario on Vimeo.
Details of the hack:
To access the password page the appendage is /model/__show_info.php?REQUIRE_FILE=/var/etc/httpasswd
To search for Dlink Routers on Shodan the query is Mathopd/1.5p6 country:MY
I’ve alerted TM to this much earlier, in August 2013 actually, and they promised they’d fix it by the end of the year. To be honest though, I don’t blame them, your router security is your responsibility and not TMs, so I think that TM isn’t doing anything wrong by not doing anything. A user should be responsible for the security of the router, just like how you are responsible for the security of your phone–even if you did get it free from Maxis or Digi. So anyhow, in the absence of any clear action from TM, I’ve taken it upon myself to inform you of the router vulnerability, and here’s hoping you do something to fix it.
As always–stay secure.
To address the issue check out my post on how to prevent this on your Unifi router, click on my post here.