Last week was a pretty exciting week for me--it was my first time on TV.
A TV show called VBuzz that was hosted on a Astro Channel 231 called me to be a guest to talk about Cyber Security, obviously I make it point to try new things and let's be honest....how many of you would turn down a chance to be on TV? I mean this is Television, if you're on it you must be good right?! Even if it is a Tamil channel, and it's on at 9pm, I thought this would be exicting...and it was!
Anyway, they scheduled me in for a show on Tuesday, and I happily took some time off work to go down to their studio and all was really great. Until....
The first thing they told me was that I couldn't talk about the recent MAS hack, because they were afraid. The Obvious question I had was--afraid of what? Apparently, MAS was a Government Linked Company, and they couldn't talk bad about a GLC for fear of losing their license. Now I had no intention of talking bad about MAS, just trying to help people understand what happened in the hack, but they were still afraid. So OK, you can still have a 15 minute conversation about cyber security without talking about MAS...no problem.
So I got my 'HD' make-up on, because High Definition recording captures so much detail of your face, that they need special make-up for it. I found that quite amusing, plus I never knew so much effort and co-ordination went into making a production like this.
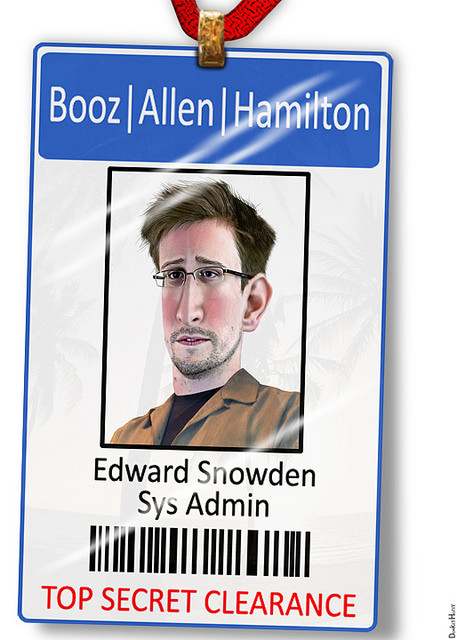
We started off with 'easy' topics like cyber criminals and hacking incidences, and the conversation was light and flowed pretty well, but then (according to plan) we veered into cyber warfare, which was a topic I was deeply into over the last few weeks. And out pop-ed a question like "What can governments do to ...." to which I responded that "Governments were the biggest perpretators of the crime". This didn't sit well with the producers or the writers, and at the end of the show we did a re-take of that bit, censoring out a my statement, which I maintained wasn't just true, but totally consistent with the entire show.