The new Prevention of Terrorism Act (POTA) in Malaysia should not be considered in isolation but rather in the context of the 6 other anti-terrorism Bills that were concurrently proposed. All of these new laws, will almost certainly come into effect, thanks to the whip system employed by the ruling party. Yet the laws violate fundamental human rights, such as a right to fair trial and right to personal privacy.
I’m particularly worried about the amendments to the Security Offenses Special Measures Act (SOSMA), an amendment that has slipped under the radar simply because its been out-done by harsher changes to the sedition act, and the new POTA.
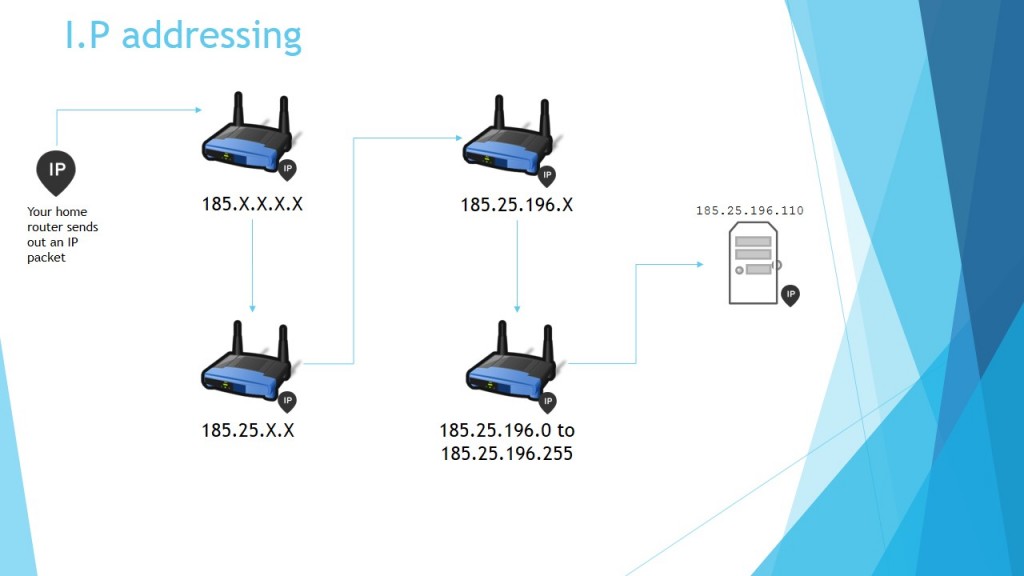
The original SOSMA had granted Law Enforcement powers to intercept and store any kind of communication, including digital communications, without any judicial oversight. Police Officers ‘not below the rank of SuperIntendants’ could wiretap any communications if the ‘felt’ there was need to do so, without obtaining any warrant. Section 24 of the act further stipulated, that law enforcement did not have to reveal how they obtained such information and could not be compelled to do so under the law, which acts as blank cheque to the police and other investigative bodies to utilize any and all manner of surveillance and intelligence gathering, regardless of their legality of their methods, since no oversight can be carried out on their methods.
The amendment to SOSMA, further enhances existing powers to allow for any evidence “howsoever obtained, whether before of after a person has been charged” to be admissible in a court of law. Which isn’t a big jump from where we were, but making this statement explicit in the act, leads me to only one conclusion.
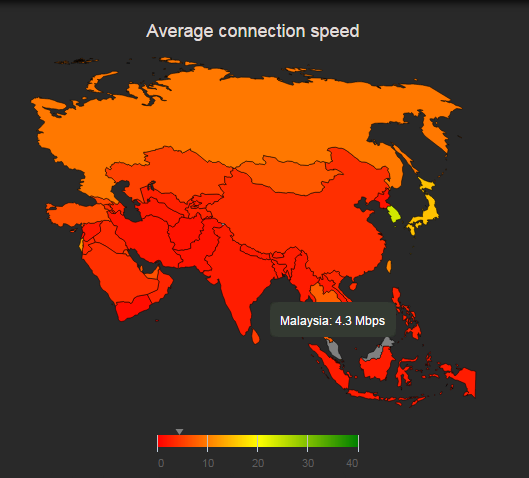
Our legislators have granted such a broad powers to the Police and the executive branch of government, that they now can intercept, and store communications of millions of Malaysians, hence the next logical step would be state-wide bulk surveillance. In light of what the NSA and GCHQ have already done, SOSMA would make it perfectly legal for Malaysian authorities to execute identical surveillance programs locally and have all the evidence generated under such program be admissible in a court of law without ever revealing how the evidence was obtained.
Think about it, on the one hand, the Government amends Sosma to allow it to collect just about anything as evidence without any Judicial oversight that might ‘slow down the process’, and on the other hand it needs POTA to detain ’terrorist’ without a trial because its hard to come by evidence. It doesn’t make any sense, what’s the point of creating POTA if you’ve already removed all the barriers to collecting evidence, and what’s the point of SOSMA if you already have the powers to detain someone without any evidence.
It would seem to me, that by allowing Government surveillance of any kind, and by allowing detention without trial, we’re creeping into a world where the Government can intercept all your communications to learn about what you’re thinking and doing–and then detain you without any justification. That’s a world even Stalin would envy.
I know I’m a tin-foil hat wearing conspiracy nut, and I know I’m on an extreme edge when it comes to political and social views—not many Malaysians agree with me on many things. Still…I think that if you look at the acts in totality, place it in context of the current trends of Government surveillance across the world, and consider that our government has a track record of deploying spyware in Malaysia, seems perfectly reasonably to me, to conclude that our government wants to run a state-sponsored bulk-surveillance operations in Malaysia.