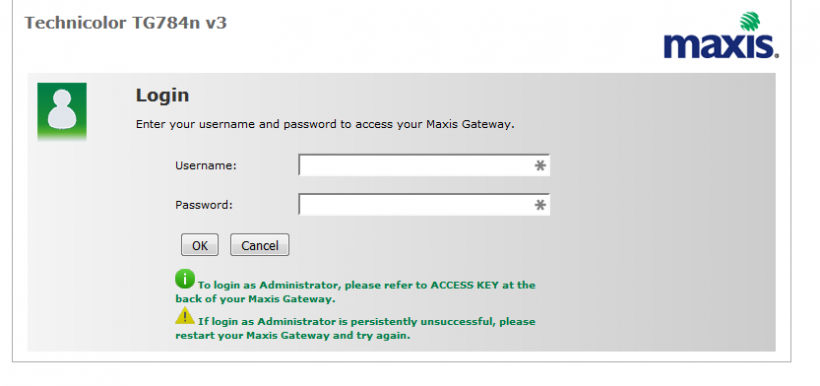
[caption id=“attachment_5307” align=“aligncenter” width=“550”]

Pic from TheMalaysianInsider, Tip to newsmen: Next time blur out the photos and names on the ID tags as well.[/caption]
There is no greater danger of tech illiteracy, than the way we treat hackers. A society that doesn’t understand technology will view those who can manipulate it as wizards and sorcerers.
Technology sufficiently advanced is indistinguishable from magic, and to most people that bar of being ‘sufficiently advanced’ isn’t set very high.
The magic analogy is apt, even in fiction, wizards are treated either with awe, ala Harry Potter and the muggles, or disdain ala the Salem witch trials, where ignorance bred fear, which in turn led to persecution.
Regular readers of this blog will know Kevin Mitnick, the grand-daddy of hackers, who was once rumored to be able to launch a nuclear missile by whistling into a phone. Not only was the rumor patently false, it nudged Judges in American courts to deny him a bail hearing, something guaranteed to Mitnick by the countries Federal Constitution. Prosecutors quickly learnt that if you throw around words like Hacker and Nuclear, Judges will willingly jettison constitutional protections quicker than Han Solo can dump cargo to make the jump to light speed.
In the absence of a nuclear threat, law enforcement agencies have begun using terrorism, and found it equally effective in demonizing hackers and anyone else who could do seemingly magical things with bit and bytes on a computer screen.