[box icon=“chat”]
Data is the natural by-product of every computer mediated interaction. It stays around forever, unless it’s disposed of. It is valuable when reused, but it must be done carefully. Otherwise, its after-effects are toxic. - Bruce Scheneier
As society moves towards a ‘knowledge’ based society, data naturally becomes a by product. Every action you perform leaves a tiny digital trail like breadcrumbs in the forest, and just like though breadcrumbs each individual data point is insignificant, but piece them together–and you’ve found you way home.
What we use to buy we cash, we now buy with credit cards – with every swipe, digital data is created and stored, it records the amount of the transaction, where the transaction took place, and the banks bill the customer, which means it can tie it to an address a person, their age, their income and even their preferences.
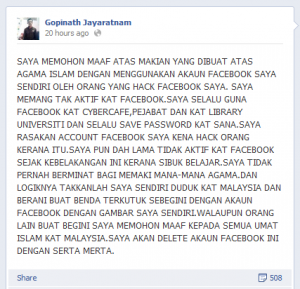
Photos were physical things we could only share in person,but now we share them digitally on social networks–all those photos are stored–permanently, and they’re tagged with meta data regarding the photos location and the names of people in the photo. A lot more data, and a lot more public. Even if you randomly stumbled across a photo on Facebook, chances are you could easily find out who the people in the photos were, and where the photo was taken–that wasn’t the case before digital photography.
When we use to pay toll booths in cash, we now use touch N’ Go, so there is a full blown record of where we travelled and at what time. Coupled with the CCTV footage they can even identify which vehicle you used. Tie that with your credit card and we can determine where you fueled before you got on the highway, coupled with CCTV footage from the Fuel station we know how many people were in the vehicle. Look at the JPN records and we’ve got the car owners name, and contact information, a quick search on Google reveals his profession on LinkedIn, his favorite places from tripadvisor, his friends on facebook, and if we pay close enough attention to his tweets chances are we can find out which football team he supports or which political party he’s aligned to.
What used to be something you’d only reserve for your close friends at the kopitiam now is public knowledge, provided some one takes the trouble to Google your name.
And the list literally goes on and on, and all these add the amount of our personal data stored digitally online–data that can be used to determine who you are, where you are, what you like, what your political beliefs and religious inclinations–even your medical history and sexual orientation. I’m not kidding, there’s a story I love to link to which tells of a supermarket who knew a teenager was pregnant before her father did.
One of the biggest abusers of personal data has been advertising companies and mail-order folks, the people that spam you day in and day out with emails about viagra and cheap housing loans, however as time goes on a lot of other people are getting on board, like insurance companies who want to know more about your medical history or driving records, banks who wish to determine if you’re really eligible for a loan–even a supermarkets may have a direct interest in your personal data.
It has become imperative that we as users look towards protecting our data online, but there also is an imperative for governments to regulate the way our data can be used–even by governments themselves (or ESPECIALLY by the government).