I read a brilliant article on the Evidence act by Zul Rafique and Partners that I think everyone should read. In it, the author compares the newly amended Evidence Act (supposedly amended to combat the evils of the internet) to a sub-section of the original act meant to look into telegraphs. Now I must admit, that as an internet kid, I don’t quite understand the concept of a telegraph, but the point is that even before the internet Anonymity was possible.
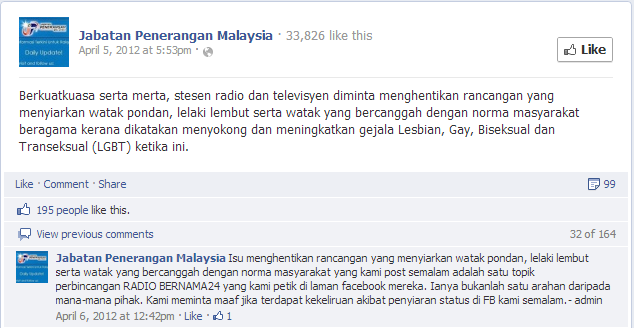
The public perception that is reinforced by ignorant government statements, is that with the internet has enabled anonymity which in turn has enabled crime.
According to Datuk Seri Mohamed Nazri Aziz, Minister in the Prime Minister Department, the amendments were tabled to address the issue of Internet anonymity since this very fact makes it extremely difficult, if not impossible, to trace the alleged offender.
That is a false statement.
Let me introduce you to snail-mail.

In the past, long before the internet was around, people use to communicate via letters and postcards that were hand-delivered by postmen to your doorstep. This is a foreign concept to most children but it’s good to let them know just how hyper-connected they are in relation to their parents or grandparents.
When you send a letter, you write a note on a piece of paper, sign it at the bottom (presumably with your name) and then place it into an envelope. You then write the name and address of the recipient on the envelope, afix a stamp (that acts as a proof of purchase)–and then drop it off at any post office you see fit. The Post Office then somehow routes that letter to the recipient on the envelope–physically hand delivered.
Notice–you never have to prove your identity when you send a letter or postcard. No where in the chain of events are you ever asked for your IC or phone number, in fact I could just as easily write a malicious letter, post it to the Prime Minister and sign it as Datuk Seri Mohamed Nazri Aziz. Would the Prime Minister then automatically assume his cousin sent him the letter just because it was signed in his name?
I guarantee you it’ll be harder for the authorities to trace that physical letter as opposed to a similar digital email. Too many people watch CSI these days to believe that statement, but there’s a reason why kidnappers still use physical constructs–because in the digital world you always leave a trace.
If we apply the amended Evidence Act to the letter analogy, Datuk Seri Mohamed Nazri would be charge for sending that malicious letter to the Prime Minister–even though he never wrote it. All of us understand the stupidity of assuming someone sent you a letter just because the letter was signed by that person, yet we seem to think nothing of it in terms of emails. In fact, if I wanted to get Nazri into a whole heap of trouble, all I’d have to do is send 1000 similar letters to 1000 different people, and sign it with his name–in that way, he’d be charged 1000 different times in a 1000 different court proceedings and even though he might be deemed innocent on each count, it’s still a whole load of trouble I can cause for him for the price of 1000 stamps (roughly Rm500 which wouldn’t pay for even one hour of a lawyers time).