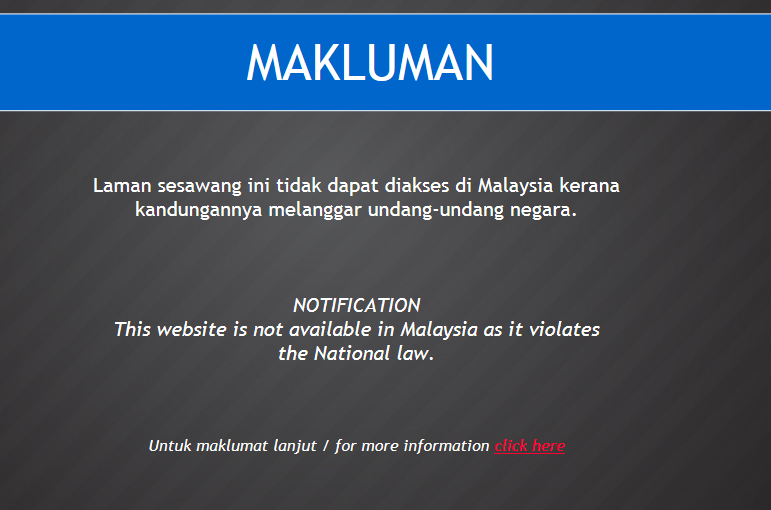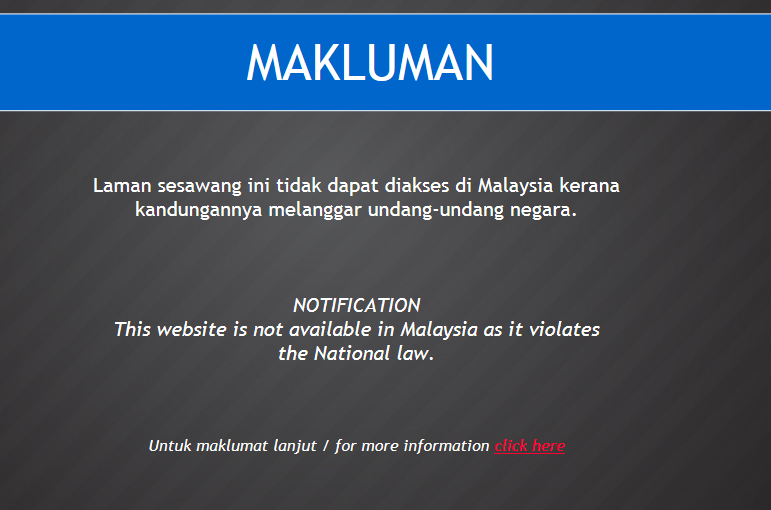
So the buzz around twitter is that Medium.com has been blocked by the Malaysian Authorities, and guess what? It’s true.
It was expected, after all Medium is where the ‘infamous’ Clare Rewcastle Brown uploads her articles to circumvent censorship of her own site, the equally diabolical SarawakReport.org.
Medium is like twitter without the character limits, and it's quite a cool site to just browse around and look for interesting articles to read, The platform claims to be "community of readers and writers offering unique perspectives on ideas large and small".
A lot of successful writers and bloggers have taken to Medium to host their content, including Stephen Levy, the author of
In the Plex, one of my favorite books on Google. He's using it (and
only it) to start a Tech Hub for his content, and placing it alongside millions of other articles contributed by both professional and amateur writers.
So it made sense for SarawakReport to take their content to Medium. After all, most of their readership is Malaysian, and since Malaysian ISPs ‘censored’ their content, using a neutral ‘un-censored’ platform like Medium was a perfect solution—well almost perfect!
It’s a phenomenon called ‘collateral freedom’, and for a while SarawakReport readers, and Malaysian internet users enjoyed that collateral freedom, Medium was free and un-censored, which made Sarawark also free and un-censored as long as it was on the platform.